Originally published on PSATEC.com
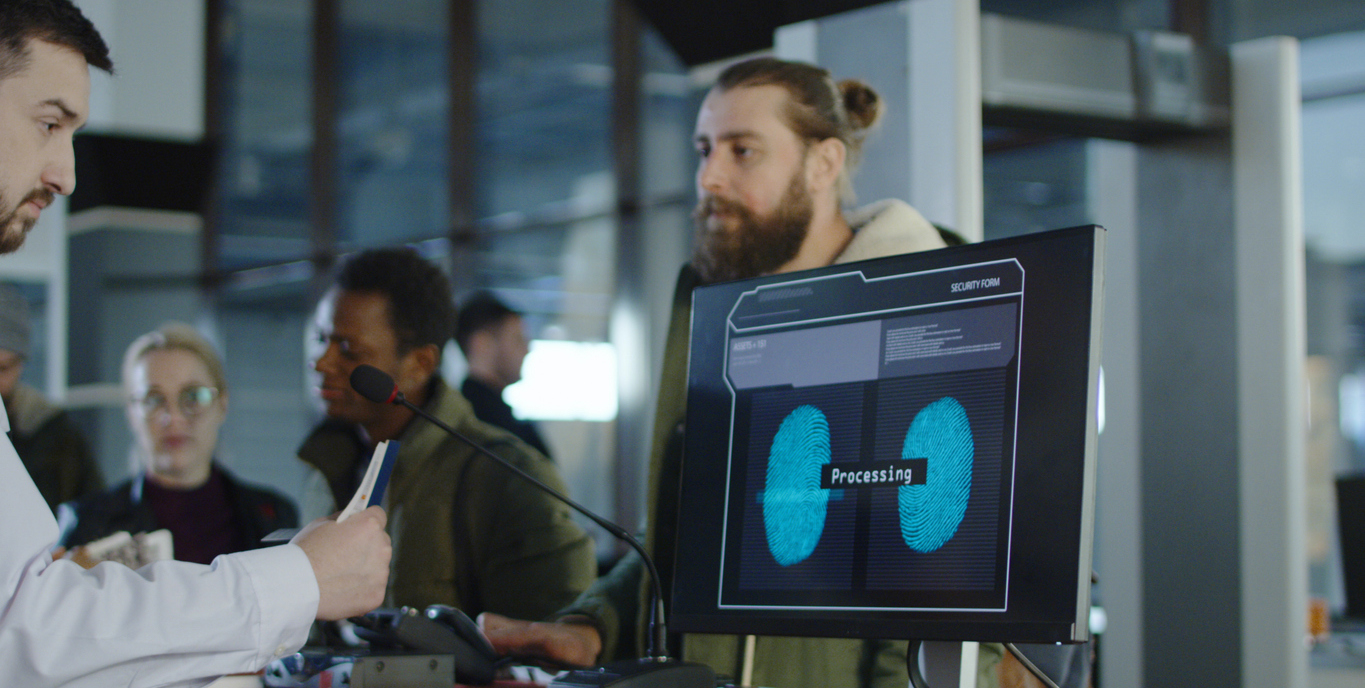
Smart cities, high-end retail stores and financial institutions are increasingly relying on advanced video surveillance systems with artificial intelligence to amplify crime prevention efforts and business efficiency. By capturing data — including thumbprints, iris patterns and license plate numbers — security systems can conduct important functions such as identifying VIP customers or blacklisted personnel.
However, the collection of this personally identifiable information has warranted a new cybersecurity standard for security technology providers and system integrators.
Placed into effect in May 2018, the General Data Protection Regulation (GDPR) is the most significant data privacy legislation in decades. It regulates the gathering, processing, distribution and storage of personal data, including video surveillance personal identifiers that are produced from AI computing.
GDPR holds service providers responsible for securing data
Most notably, GDPR holds service providers responsible and accountable for securing this data, even subjecting them to fines for data breaches. Recently the National Data Protection Commission, a French authority, imposed a significant fine on a cloud service provider for what it called a “lack of transparency, inadequate information and lack of valid consent” regarding ad personalization for users, which it deemed to be noncompliant with GDPR standards.
For security professionals, the greatest cyber risk for surveillance data is that it will be accessed and stolen through the endpoints, edge or network itself. Many cybersecurity discussions have centered around securing “data in transit” and applying strategies like end-to-end encryption. However, it is essential that system integrators also deploy solutions that secure “data at rest.”
Implementing cyber-hardening protocols
Safeguarding “data at rest” starts with implementing cyber hardening protocols for hard drives and SSDs, and integrators have a critical responsibility to understand which technologies yield the highest performance and reliability. Software encryption, pseudonymization, hardware encryption and secure erase are the most effective mechanisms to secure data. Self-encrypting drives are an especially attractive option because if a breach occurs, a company does not have to publicly report the incident if the data is encrypted, according to GDPR. This can save customers thousands of dollars in crisis communications and reputation damage.
While GDPR currently affects the security channel who have customers in the European Union, other cities, states and countries are already starting to follow suit by introducing similar policies.
The time for integrators and IT professionals to be trained in surveillance data security measures is now.
For a more in-depth look at the top cyber vulnerabilities for surveillance systems and data security best practices, join me at TEC. Attend my education session on Wednesday, March 13, at 3:30 pm as I discuss, “Securing Your Data for the New Wave of Industry Regulation.” You can also stop by Seagate Technology’s booth on Thursday, March 14, for specific application questions.